A keylogger is a device or technology considered a form of malware or hardware that tracks and records successive keystrokes performed on a keyboard. It does this by tracing and sending information to the hacker using command-and-control (C&C) servers. It typically operates in a covert fashion so that potential victims do not suspect that their activities are being monitored.
Hackers can use this tool to record their target’s browsing activity and obtain their personal information, which they can use to blackmail the target, withdraw money from their bank account or sell the information to other cybercriminals on the dark web. can do for Can do so for their own financial gain.
Types of Keyloggers
Depending on which part of the computer they are embedded into, all keyloggers can be categorized as either software-based or hardware-based. The five most common types of keyloggers across both these categories include the following:
API-Based Keylogger –
API-based keyloggers are by far the most common. These pieces of keylogging software use the Keyboard API (short for Application Programming Interface) to record your keystrokes. Every time you press a key, a notification is sent to the application you are typing so that the typed character appears on the screen. API-based keyloggers intercept these information and capture each of them as a separate event. The logs are kept in a file on the system hard drive for easy recovery by the hacker.
Form Grabbing-Based Keyloggers –
Instead of logging each keystroke separately, form grabbing-based keyloggers log data from your web form upon submission. Similar to API-based keyloggers, they intercept submission notifications to log all the information you entered into the form. This may include your full name, address, email phone number, login credentials or credit card information. The whole process is completed as soon as you hit the “Submit” or “Enter” button and your form data is submitted to the website.
Kernel-Based Keylogger –
As the name suggests, kernel-based keyloggers obfuscate the core of your computer’s operating system (also known as the kernel), making them very difficult to detect and remove. They hide inside your operating system and record your keystrokes as they pass through the kernel. Because they are more difficult to write, these keyloggers are rarer than other software-based varieties. They are distributed through rootkits, malicious software bundles that can bypass your computer’s kernel and target hardware.
Hardware Keyloggers –
Hardware keyloggers are devices that use circuitry inside a keyboard to log keystrokes. They are often built into keyboards, although they are also available as USB connectors (for personal computers) or mini-PCIe cards (for laptop computers). Rather than relying on software to store logged keystrokes, all records are kept in the device’s internal memory. However, this also means that hackers must have physical access to the keyboard in order to retrieve this information.
Acoustic Keylogger –
Acoustic keyloggers are very complex and are therefore rarely used. They use the principles of acoustic cryptanalysis to record your keystrokes at the hardware level. No matter which keyboard you’re using, each of its keys has a unique acoustic signature. The differences are subtle, but individual signatures can be determined by analyzing a sample through various statistical methods. However, not only does this take a lot of time, but the results may not be as accurate as other types of keyloggers.
How are Keyloggers Constructed ?
The primary concept behind keyloggers is they must be placed between when a key gets depressed on a keyboard and when the information regarding that keystroke appears on the monitor. There are several ways to accomplish this.
Some hackers use video surveillance to see the connection between the pressed keys and what appears on the monitor. A video camera with a view of the keyboard and the screen can be set up. Once it records a video of the keystrokes and the login or authentication screens the strokes have to get past, the hacker can play the video back, slow it down, and see which keys were pressed.
An attacker can also put a hardware bug inside the keyboard itself. This would record each stroke made and send the information to be stored, either on a server or nearby physical device. It is possible for a keylogger to be placed within the wiring or inside the computer—as long as it is between the keyboard and the monitor.
Additionally, keylogger software can be designed to intercept all input that comes from the keyboard. This can be done using a few different methods :
- The driver that facilitates the interaction between the keyboard and the computer can be replaced with one that logs each keystroke.
- A filter driver can be positioned within the keyboard stack.
- Kernel functions, which use similarities between data to assist machine learning, can be intercepted by software keyloggers and then used to derive the necessary keystrokes to perform authentication functions.
- The functions of the dynamic link library (DLL), which stores code used by more than one program, can be intercepted.
The software, which is recognized as a form of spyware, is built using a few different methods. Here are the most common:
- A system hook, which is a technique for altering the operating system’s behavior, is used to intercept each notification generated whenever a key is pressed. This kind of software is typically built using the coding language C.
- A cyclical information request is set up that gathers information from the keyboard. These kinds of keyloggers are typically written using Visual Basic or Borland Delphi.
- A filter driver is written in C and installed inside the computer.
As a sort of defense mechanism, some keyloggers, referred to as rootkits, have the ability to disguise themselves to slip manual or antivirus detection. They either mask in user mode or kernel mode.
Way to Detect Keylogger on Any Computer –
Keyloggers are dangerous programs that hackers install on any system to sniff passwords, credit card details, etc. It stores every keystroke of the person using the computer and thus provides some of its most important information to hackers. Some friends also install keyloggers program just to hack facebook password etc. Whatever the case, if you are using a computer with Keylogger installed, you are at serious risk of losing sensitive information which can also lead to financial loss. Even if it’s your computer, it could be used by a creepy friend of yours who has the wrong intention of stealing your data.
Below is a sample keylogger generated txt file and you can easily see how capable it is of extracting what you type on your PC.
Some people say that it is easier to find the keylogger by searching .txt files in Program Files, but this is not true. The hacker may have deleted it after sending it online. Also file formats can be manipulated.
How to delete a keylogger ?
Some types of keyloggers are easily detected and removed by the best antivirus software (like Norton, BitDefender, Intego or Panda), but some others may prove very difficult to identify and isolate from your system. That’s because many software-based keyloggers are designed like legitimate software and are thus able to bypass most antivirus or anti-malware programs. To make matters worse, some keyloggers run at a higher level of privilege than standard cybersecurity software, which makes them next-to-impossible to detect and remove.
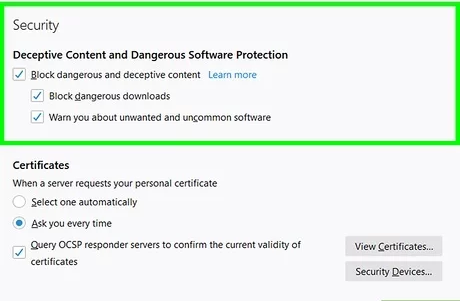
If you suspect that someone may have installed a keylogger on your computer but your anti-malware software isn’t detecting anything, you may be able to find it in Windows Task Manager. Simply launch Task Manager and take a close look at the list of active processes to see if there’s anything out of the ordinary. If necessary, ask someone tech-savvy to help you with this step. You can also check your system’s firewall for any suspicious activity, such as unusual amounts of incoming and/or outgoing data.
As with all other cyber threats, the best way to stay safe from keylogger attacks is to use the best antivirus software and run regular scans of your computer. To ensure that you’re protected against the latest threats, you should configure your antivirus program to automatically download virus definition updates. Finally, don’t open any links or attachments included in suspicious emails as they might initiate an “invisible” download of a keylogger, spyware, adware, or some other type of malicious software.
Click here to know more about this – how to enable steam overlay